How does NVE and NAE encrypt data?
Applies to
- ONTAP 9
- NetApp Volume Encryption (NVE)
- NetApp Aggregate Encryption (NAE)
Answer
NVE and NAE is comprised of three Components:
-
Software Cryptographic Module (CryptoMod)
- Performs the data encryption operations and generates encryption keys for the volumes (see Figure 1).
Figure 1) NVE and NAE encrypt/decrypt flow
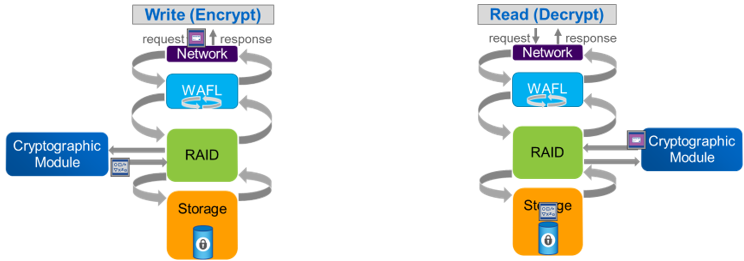
- Performs the data encryption at the RAID layer, which allows the storage efficiencies to work. After a read operation, data is unencrypted when the data leaves the RAID layer.
-
Encryption Keys
- A unique XTS-AES-256 data encryption key is generated for each volume or aggregate for NVE and NAE respectively.
- When using the onboard key manager (OKM), an encryption key hierarchy is used to encrypt and protect all volume or aggregate keys. These encryption keys are never displayed, shown, or reported in an unencrypted format.
-
Key Manager
- Stores all encryption keys used by ONTAP
- Can be the onboard key manager (OKM) or an external key manager that uses the OASIS Key Management Interoperability Protocol (KMIP).
Comparison with NetApp Storage Encryption
- NSE requires all drives in an HA pair to be purpose-built, self-encrypting drives. These drives perform the data encryption themselves through a hardware-accelerated mechanism. Because of the hardware acceleration, NSE systems usually outperform NVE systems when encrypting data.
- NSE drives are FIPS 140-2 level 2 validated, and the CryptoMod used by NVE and NAE are FIPS 140-2 level 1 validated. FIPS 140-2 level 1 is the highest attainable level for a software module.
Note: The software CryptoMod generates authentication keys for the self-encrypting drives
Additional Information
