Prerequisites for enabling SAML authentication in AIQUM
Applies to
- Active IQ Unified Manager (AIQUM)
- Security Assertion Markup Language (SAML)
Description
Terminologies
- Active IQ Unified Manager server is being tested against the following IDP servers only.
- Microsoft Active Directory Federated Services (ADFS)
- An identity provider developed by Microsoft. It can run on Windows Server operating systems to give users single sign-on access to systems and applications located across organizational boundaries
- open-source Shibboleth
- Shibboleth is an open-source project that provides single sign-on capabilities. It allows sites to make informed authorization decisions for individual access of protected online resources in a privacy-preserving manner
- Microsoft Active Directory Federated Services (ADFS)
- Security Assertion Markup Language (SAML)
- An open standard for exchanging authentication and authorization data between parties—in particular, between an identity provider and a service provider. As its name implies, SAML is an XML-based markup language
- Single sign-on (SSO).
- After a SAML IdP authentication, the IdP issues a SAML assertion, and redirects the administrator’s web browser back to UM. UM processes the SAML assertion, and then looks up the authorization role from its internal database. The session is established and UM returns a SAML session token to the administrator’s web browser. The IdP is configured with a default lifetime of 2–8 hours for the secure SAML token. These are over writable by relying-party-specific setting.The administrator is allowed access to UM for the lifetime of the token
- Claim rules.
- Claim rules provide a mechanism for mapping IdP-defined attributes to a relying party. These attributes—such as a user ID or common name—are used by the relying party to map authorizations after IdP authentication.
- IDP (Identity Provider) Requirements
| Claim Rule | Value |
| SAM-account-name | Name ID |
| SAM-account-name | urn:oid:0.9.2342.19200300.100.1.1 |
| Token groups – Unqualified Name | urn:oid:1.3.6.1.4.1.5923.1.5.1.1 |
Note: the claim rules mention above needs to be configured/setup in IDP server. IDP server setup is solely done by IDP admin. NetApp support is not involved setting up IDP server.
Ports, local users setup and other configuration:
- Ports (443 or 80) needs to be open between Active IQ Unified Manager and IDP server
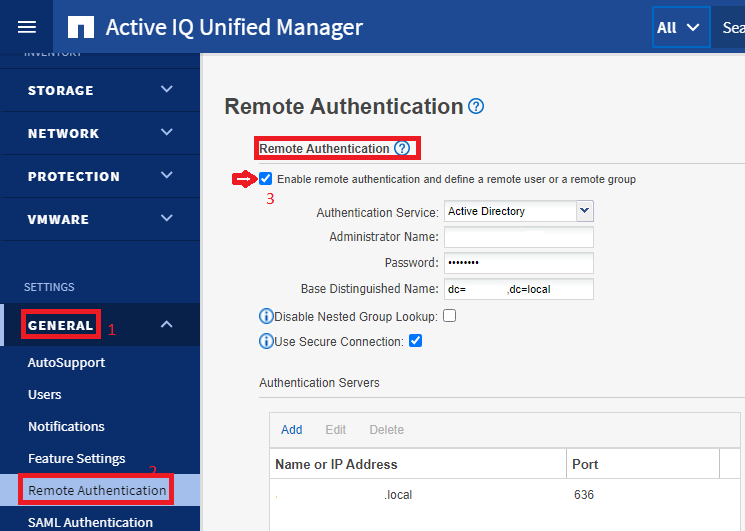
- We must configure Active IQ Unified Manager "Remote Authentication" first before we will configure SAML authentication
- To configure "Remote Authentication" in Active IQ Unified Manager, please follow this KB.
- Confirm remote authentication enabled using UM CLI
um cli login -u <maintenance_user>um option list | grep -i "auth.ldap.enabled"- Note: "true" output is ldap is enabled
- You can confirm the same using UM Web UI
- Confirm if you are able to log on to Unified Manager server as Active Directory Domain User
- Note: If remote authentication is enabled but "remote user" or "remote group" was not added then you cannot enable "SAML Authentication". This is why it is important to enable "remote authentication" and then log on as domain user to unified manager.
- DNS
- Active IQ Unified Manager should be able to ping IDP server fully qualified domain name
- IDP server should be able to ping Unified Manager fully qualified domain name
IDP CLI --> ping <Active_IQ_Unified_Manager_FQDN>
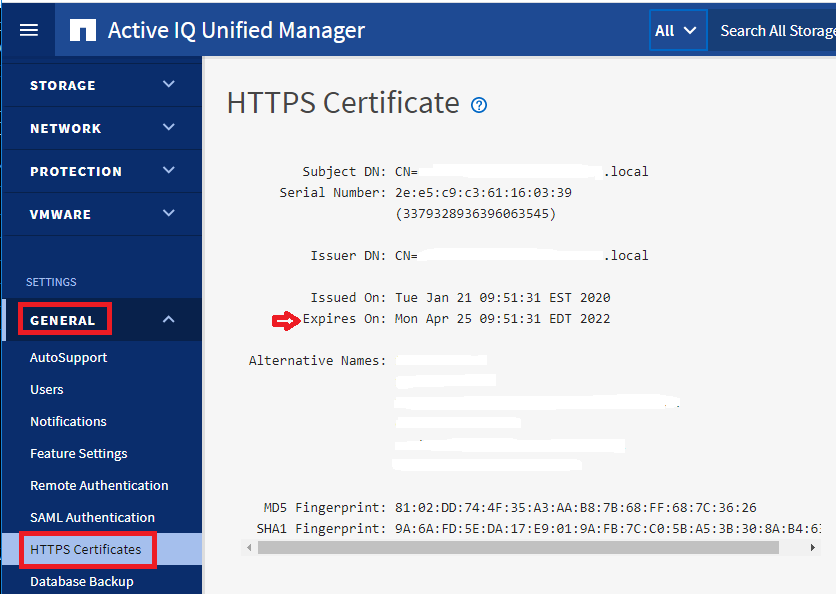
- Check to make sure Unified Manager certificate is not expired
- Two ways you can check that, UM webUI and UM CLI
- UM CLI:
dfm cli login -u <maintenance_user>dfm ssl server detail
- UM Web UI:
- UM CLI:
- Two ways you can check that, UM webUI and UM CLI
- IDP (Identity provider) URL
- Please capture the IDP URL from ADFS or Shibboleth server, We will need this URL to configure SAML on Active IQ Unified Manager.
Additional Information
Parent topic: SAML setup and troubleshooting in Active IQ Unified Manager
