Witness protocol connection fails if the client does not use NTLMv2
Applies to
ONTAP 9
Issue
- When configuring a Continuously Available (CA) share to be used in Hyper-V deployment, the witness protocol fails and Windows generates the following event log entry:
Witness Client failed to find a Witness Server for NetName \ccp1filer with error (A remote procedure call (RPC) protocol error occurred.). Retrying in (15) seconds
- While connecting to a CA share from a Windows Server 2012 R2 client, the user can map the share successfully and create / view files; however, the SMB 3.0 Witness Protocol fails.
Windows SMBWitnessClient Event Log:
Log Name: WitnessClientAdmin
Source: Microsoft-Windows-SMBWitnessClient
Date: 12/25/2016 8:18:41 PM
Event ID: 6
Task Category: None
Level: Critical
Keywords:
User: NETWORK SERVICE
Computer: c1slic01.ccp1.gene.com
Description:
Witness Client failed to find a Witness Server for NetName \ccp1filer with error (A remote procedure call (RPC) protocol error occurred.). Retrying in (15) seconds.
- secd log:
[kern_secd:info:4681] .------------------------------------------------------------------------------. [kern_secd:info:4681] | RPC FAILURE: | [kern_secd:info:4681] | secd_rpc_auth_msrpc has failed | [kern_secd:info:4681] | Result = 0, RPC Result = 2147483651 | [kern_secd:info:4681] | RPC received at Sat Jan 7 17:12:51 2017 | [kern_secd:info:4681] |------------------------------------------------------------------------------' [kern_secd:info:4681] Failure Summary: [kern_secd:info:4681] Error: MsRPC authentication procedure failed [kern_secd:info:4681] [ 0 ms] Login attempt by domain user 'CCP1\C1SLIC01$' using NTLMv1 style security [kern_secd:info:4681] [ 0] Successfully connected to 10.34.62.1:445 using TCP [kern_secd:info:4681] [ 10] Successfully authenticated with DC ccp1sdc01.ccp1.gene.com [kern_secd:info:4681] [ 12] User authenticated as a domain user [kern_secd:info:4681] **[ 12] FAILURE: Error case not correctly journaled
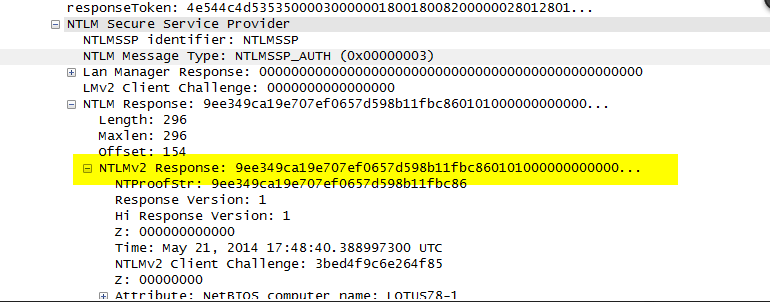
- In packet trace capturing the Witness Protocol handshake, the absence of NTLMv2 is noted during client NTLMSSP_AUTH:

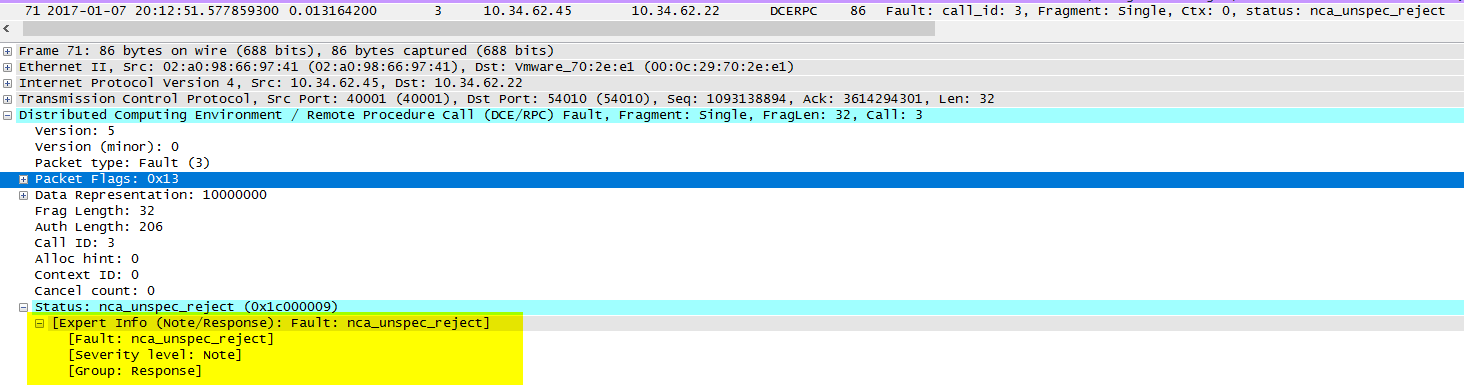
- Response from SVM
- By comparison, successful Witness Protocol handshake, NTLMv2 presents itself as follows: