How to disable SSLv2 and SSLv3 in SnapManager for SharePoint
- Views:
- 513
- Visibility:
- Public
- Votes:
- 3
- Category:
- snapmanager-for-microsoft-sharepoint
- Specialty:
- legacy
- Last Updated:
Applies to
SnapManager for Microsoft SharePoint Ser
Answer
Perform the following steps to disable SSL versions 2 and 3 for use by SnapManager for SharePoint (SMSP) to remove exposure to CVE-2014-3566, also known as POODLE.
How does CVE-2014-3566 affect SMSP?
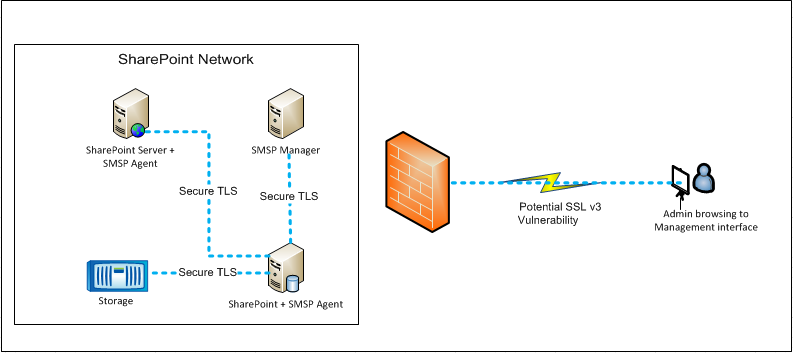
The ideal candidate for this threat is content being accessed over public Wi-Fi or insecure networks. In this case, a man-in-the-middle attack is a potential risk, since communications over SSL between an end-user and software could expose user credentials, passwords, and other information. While this issue is not fundamentally with SMSP, it leverages Microsoft technology such as Internet Information Services (IIS) server and Microsoft Windows security provider which have SSLv3 and TLS enabled by default. The SMSP Manager-Agent or Agent-Agent communication will always negotiate communications over TLSv1 or later.
Take the following precautionary measures to remove exposure to CVE-2014-3566:
- Follow Microsoft best practices for disabling SSL on SMSP 7.x / 8.x Manager and Agent servers:
- To disable SSLv3, see Microsoft Security Advisory 3009008
- To disable SSLv2, see How to Disable SSLv2 on a Windows Server 2008 and Windows Server 2008 R2 Domain Controller (dsforum2wiki)
Note: SMSP Agents always communicate over TLS and are not subject to this vulnerability.
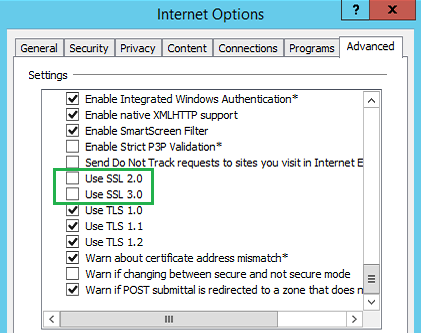
- As an end-user, update Internet Explorer (IE) browser settings to disable SSL:
- Launch Internet Options from the Start Menu
- Click the Advanced tab
- Uncheck Use SSL 2.0 and Use SSL 3.0
How to disable SSL in SMOSS V6.x or earlier legacy software
For the Apache/Tomcat based platforms, modify the Tomcat settings on the SMOSS Manager server following these steps:
- Use the service management tool to 'stop' the Web Service.
- Edit the
'server.xml'document in the…\ZeusWeb\conffolder. - Find the '
sslProtocol' flag, which is set to'TLS'by default.
Note: This setting also allows for SSLv3. - Add the argument
'sslEnabledProtocols=”TLSv1”'as seen in the example below, to prevent SSL from being used.
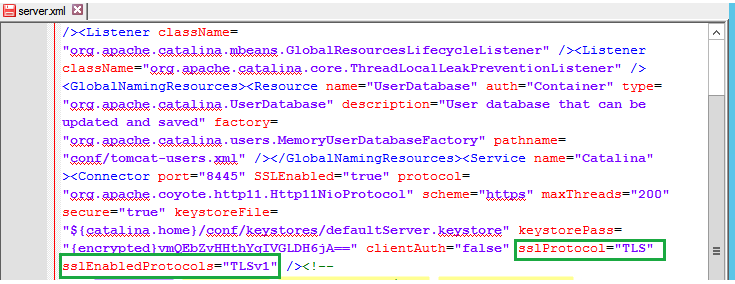
- Save the
'server.xml'file and change the file to 'read-only' to prevent other tools from modifying or reverting this change. - Start the Web Service in the service management tool.
- Test this configuration change by accessing the SMOSS management interface using a browser with only SSLv3 enabled - a successful result will be a failed connection.
Additional Information
N/A
